The COVID-19 pandemic has driven a significant spike in Distributed Denial of Service (DDoS) and password login attacks, according to new analysis from F5 Labs.

Based on data sourced from the F5 Security Incident Response Team (SIRT), the research reveals an “unprecedently febrile and vulnerable threat landscape” post-lockdown.
“F5 Labs reviewed all the reported incidents from the beginning of 2020 until August, and attackers are clearly doing everything they can to exploit pandemic-related online behavior,” said Raymond Pompon, director of F5 Labs.
“Expect more turbulence on the horizon as COVID-19 continues to evolve and wield an economic impact. This year’s holiday shopping season, for example, will be more online than ever and under intense fire from cybercriminals. One thing is clear: our rising usage and dependence on technology have also brought increased levels of already growing attack trends.”
Lockdowns unlocking new threats
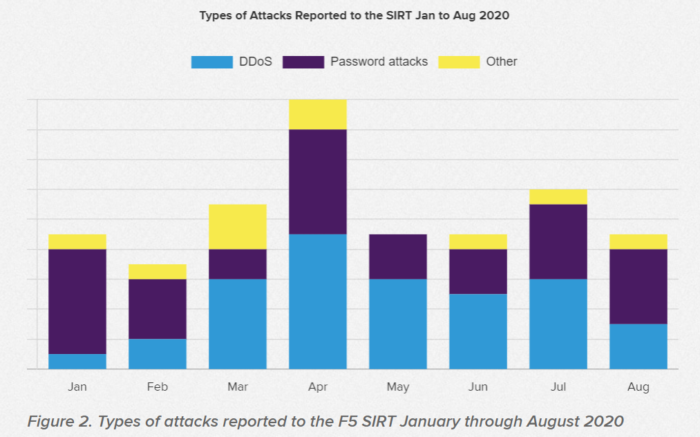
In January, the number of all reported SIRT incidents was half the average reported in previous years. As lockdowns hit from March onwards, incidents rose sharply. Numbers plateaued with a three-fold spike over previous years in April, and only began to fall back to normal in May and June. In July, they crept back up to twice the level seen at the same time in 2019.
The attacks fell into two large buckets: DDoS and password login attacks. Password login attacks were comprised of brute force and credential stuffing attacks. Both involve attackers trying guess their way past a password login.
If you liked this content…
From January through August, 45 percent of SIRT reported incidents were related to DDoS and 43 percent were password login attacks. The remaining 12 percent were reported incidents for things like malware infections, web attacks, or attacks that were not classified.
DDoS surges and shifts
In January, DDoS attacks started off as just a tenth of reported incidents. By March, they had grown to three times that of all incidents.
In 2019, 4.2 percent of DDoS attacks reported to the F5 SIRT were identified as targeting web apps. This increased six-fold in 2020 to 26 percent.
Meanwhile, attack types are becoming more diverse. In 2019, 17 percent of all DDoS attacks reported to the SIRT were identified as DNS amplification attacks, which spoof DNS requests to flood back at a victim. The number nearly doubled to 31 percent this year.
DNS Query Flood are also on the rise. This is where an attacker sends malicious requests that are purposely malformed to cause a DNS server to exhaust its resources. 12 percent of DDoS attacks during the period studied by F5 Labs used this method.
F5 Labs also observed a spike in authentication attacks on APIs, which doubled from 2.6 percent in 2019 to 5 percent so far in 2020.











